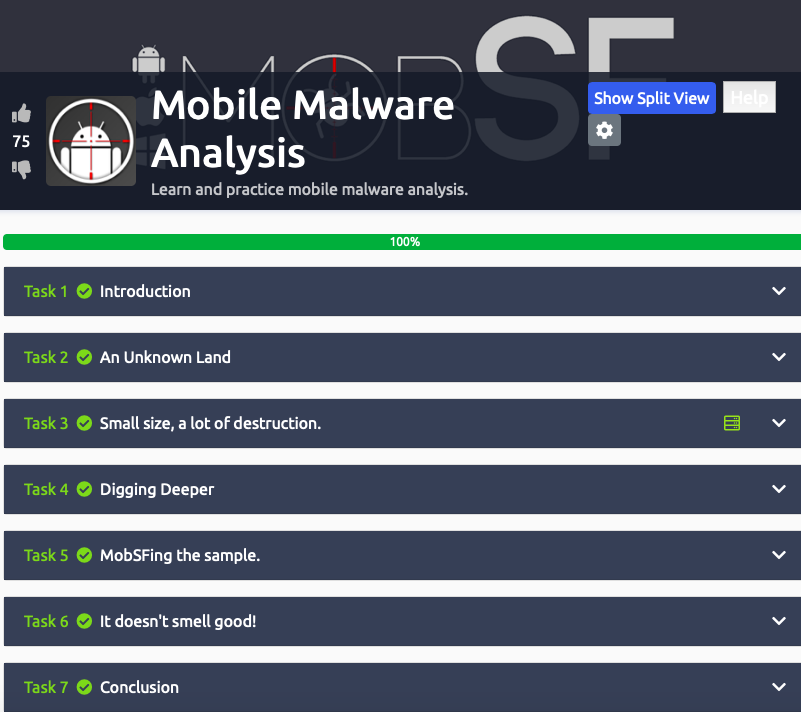
 Mobile Malware Analysis
Mobile Malware Analysis
Learn and practice mobile malware analysis
This blog is based off the Mobile Malware Analysis TryHackMe room. I’m currently studying Malware and learning how to analyze malware.
Malware is a malicious software designed to case damage to your computer, client, server, & network.
Mobile malware is malicious software specifically designed to target mobile devices, such as smartphones and tablets, with the goal of gaining access to private data.
Mobile malware is definitely on the rise, especially now, during the pandemic. More companies are remote, which means more employees will receive a mobile phone.
Task 1: Introduction
It's incredible how often our computers are in the scope of cyber attacks. Antivirus has become an indispensable shield to provide us with a more secure environment, since we are exposed to destructible malware and cyber attacks. Inside our pockets, we have computers so powerful, but much smaller, we must be equally attentive on our phones, because we can suffer equally damaging attacks, sometimes even worse, because they can store relevant information such as private conversations and important accounts.
Task 2: An Unknown Land
It is important to look at the past to understand why things are as they are today.A new technology, due to the lack of exploration, appears to be extremely reliable.
Every system is reliable, until someone proves otherwise.You will need to do some research in order to answer the questions in this task.
What known as the first malware created to affect mobile devices? Cabir
What technology does this worm used to multiply?
Bluetooth
What operating system did it infect?
Symbian
What message did it show on the screen of the infected mobile phone?
Caribe
The worm was created and sent out by researchers as a PoC (Proof of Concept), they did not believe that the mobile operating system could be easily exploited. Since then, malicious programs have become more popular.
Task 3: Small size, a lot of destruction.
Deploy the machine & use MobSF to scan the file named "TWFsd2FyZQ.apk" that is located on the Desktop.
What is the format of the file?
.APK
The sample's size is 10,1 bytes, so it seems that it is not a complex application.
Decode the name of the sample.
Malware
Here I decoded the name of the sample TWFsd2FyZQ
Using https://www.base64decode.org
The only reason I knew what to do here is because of the reading I had already been doing for the Security+ exam. I didn’t really know what to actually decode though.
Which is the target platform?
Android
I was able to find this by doing a google search on .APK
At this point I was over it. Just that one part literally took me forever.
I mean this might have been easy for some but me. LISTEN, I put my all into this. I literally googled everything on the MOBSF scan. SN: I really like the MOBSF scan. I was scared to clicked on certain things. Scared I might load my computer with malware.
Task 4: Digging Deeper
Let's make a deeper analysis.
VirusTotal is an incredible service, this web site can give us the power of analyze a package with the database of more then seventy Anti-Virus, and the result is fast and accurate.
To analyze the file in VirusTotal, you will need the file hash, you can get it by using the powershell cmdlet "Get-FileHash" or you can analyze the file with MobSF and it will show the file hash (we will get back to this tool in the next task).
What does Avast-Mobile can tell us about this software?
Android:Metasploit-G [PUP]
What program was used to create the malware?
Metasploit
The results provided by VirusTotal shows that we have a generic malware. It does not serve for attack purposes because we can see that a good part of the Antiviruses are detecting it, this malware is a good one for searching purposes, but it is also used for post exploitation.
What is the package name?
com.metasploit.stage
What is the SHA-1 signature?
74d442594acf11dc6e3492ffea5eb8956afd000d
By extracting the content, it will create a folder with some files inside, one of which is a XML. It describes some important information about the application for Android build tools, for Android operating system and for Google Play. This file declares items, shows some stuff as the package name and the permissions required to the device. The information that will be needed for the next questions can be found on VirusTotal also.
What is the unique XML file?
AndroidManifest.xml
How many permissions are there inside?
22
Which permission allows the application to take pictures with the camera?
android.permission.CAMERA
What is the message left by the community?
THM{V1ru5-T0t4al-TWFsd2FyZS1BbmFseXNpcw}
Task 5: MobSFing the Sample
Let's use MobSF(Mobile Security Framework) to make a deeper analysis of this file, MobSF is a software created to make a security focused analysis of Android and IOS files. It can check for misconfigurations, leaked data and much more in a mobile program.
This tool can be used for static and dynamic analysis, in this room we will focus only in the static analysis but you are free to install it in a virtual machine you own to understand more how the application works, you can install it in GitHub - https://github.com/MobSF/Mobile-Security-Framework-MobSF.
The machine is configured to start MobSF when deployed, if you accidentally closed the web page you can visit the MobSF page by visiting the link http://127.0.0.1:8000 inside the deployed machine. Press the "Upload & Analyze" button and select the file we have been working on.
What is the programming language used to create the program?
Java
How many signatures does the package has?
1
Application is signed with v1 signature scheme, what is it vulnerable to on Android <7.0?
Janus
MobSF gives all the code decompiled. Just a base of programming make us able to understand a little bit of what is happening.
This malware is used to create a connection with the victim that is called a reverse shell.
What is the App name?
MainActivity
It looks like there is a function calling for the package manager, so it can see all the installed applications. What function is that?
b.getPackageManager
Returning to the manifest.
The flag "android:allowBackup" allows the user to backup application data via USB debugging. It is recommended that this be set as "False", even if by default it is "True".
What is the severity of this configuration?
Medium
Task 6: It Doesn’t Smell Good!
I think that now we have the necessary knowledge to analyze bigger stuff.
Our next sample located on the Desktop, the name of the file is sample2.apk, let's start a MobSF analysis on it.
What is the SHA-256 hash of the file?
bd8cda80aaee3e4a17e9967a1c062ac5c8e4aefd7eaa3362f54044c2c94db52a
After finding the sample on VirusTotal, what does the "Avast" anti-virus enginerecognizes it as?
Android:Obfus-BM [Trj]
With what we have, try to find out the name of the sample.
Pegasus
It seems like it is a very dangerous malware and has a big history of destruction.
This became news for spying journalists, what year was that?
2017
https://en.wikipedia.org/wiki/Pegasus_Project_(investigation)
https://qz.com/india/2036207/meet-an-indian-reporter-named-in-the-leaked-pegasus-spyware-data/
It was reported that the malware was developed by a legitimate intention: The idea behind it was to use the software as a government tool designed to track and combat terrorism and crime.
This malware has been found infecting people's smartphones and political activists in more than 44 countries.
If we search the name we found of the malware in MITRE ATT&CK (https://attack.mitre.org/), we can find some interesting information.
What is the ID of the MITRE ATT&CK that is associated with our sample?
S0316
https://attack.mitre.org/software/S0316/
What technique has the ability to exploit OS vulnerabilities to escalate privileges?
T1404
https://attack.mitre.org/techniques/T1404/
Now, let's go back to the MobSF analysis.
There is a permission that when accepted, allows the application to access the list of accounts in the Accounts Service. What is the status shown by MobSF regarding this permission. (android.permission.GET.ACCOUNTS)
Dangerous
What org.eclipse.paho.client file refers to properties of Portuguese from Brazil (pt-br)?
org/eclipse/paho/client/mqttv3/internal/nls/messagesptBR.properties
This software has several features that make the identification and the processes it performs to explore the target, harder to handle, even when it is being analyzed.
The malware has a special appeal for its safety and its internal components, reducing the risk of compromise. It has a functionality for its cryptographic operations with the feature of a random bit generation service. How can it be identified?
fcsrbgext.1.1
To find this, let’s go to the NIAP Analysis in the MOBSF results
It is normal to think that our mobile phones are harder to be infected, they have characteristics that makes the malware actions limited, as the Sandbox concept, and the fact that we never download things directly from the open internet.
Here I leave some awesome articles and other rooms that may be interesting to get deeper into this subject.
https://github.com/OWASP/owasp-mstg
https://attack.mitre.org/matrices/mobile/android/
https://attack.mitre.org/matrices/mobile/ios/
https://tryhackme.com/room/malmalintroductory
https://tryhackme.com/room/androidhacking101
https://tryhackme.com/room/iosforensics
Conclusion:
Overall, I thoroughly enjoyed this room. I was literally scared to click on any links on the scans. The thought of infecting my computer with malware. It literally took me two days to complete this room. I’m ok that it took me a while to complete this room. I really took my time, did a ton of research, and learned a lot from it. There is still a ton that I need research and dig into about malware. Taking notes & snapshots along the way, was very crucial for me. I know for sure I will review this room again to gain a greater understanding of Mobile Malware Analysis. I also watched a few videos on YouTube about virustotal & MOBSF to gain a better understanding of what I’m looking at during scans/analyzers.
